Back
Blog
Insights
Axios Compromised: 100 Million Weekly Downloads, a Hidden RAT, and Why the Chain Reaction Won't Stop

Frank Lyonnet
Four days ago, we published a technical breakdown of how EDAMAME detects the Trivy→LiteLLM supply chain attack through runtime behavioral heuristics. We said the chain reaction was already in motion. We said step three was being planned.
It took four days.
On 31 March 2026, two malicious versions of axios — one of the most depended-upon npm packages in existence, with over 100 million weekly downloads — were published to the npm registry. A compromised maintainer account was used to inject a phantom dependency whose postinstall hook silently downloaded and executed a platform-specific Remote Access Trojan on every machine that ran npm install.
The attack was live for approximately three hours before npm pulled the malicious versions. Three hours on a package with half a billion weekly downloads. Do the math on how many CI pipelines, developer laptops, and production builds ran npm install in that window.
This post is a follow-up to our LiteLLM analysis. We reproduced the axios attack's behavioral pattern in our E2E test suite and confirmed that EDAMAME detects it through three independent layers — without any prior knowledge of the specific malware, the C2 domain, or the payload signatures.
The chain reaction: Trivy → LiteLLM → axios
This is no longer a pair of isolated incidents. It's a trend line, and it's accelerating:
Trivy (March 16): The security scanner — the tool watching for backdoors — was itself backdoored. Credential-stealing infostealers injected into GitHub Actions tags and releases, built to extract secrets from CI runners.
LiteLLM (March 24): Using credentials stolen from the Trivy supply chain, attackers published malicious versions of the popular LLM gateway. A three-stage credential harvester, encrypted exfiltrator, and Kubernetes worm. 3 million downloads a day. Discovered by accident — a fork-bomb bug in the malware.
axios (March 31): A phantom dependency injected into the most ubiquitous HTTP client in the JavaScript ecosystem. A platform-specific RAT with persistent C2 beaconing. 480 million weekly downloads. Discovered by StepSecurity.
The chain reaction we described in our LinkedIn post is playing out in real time:
Compromised package lands on a developer laptop
↓ SSH keys, cloud credentials, npm tokens harvested silently
↓ Same package runs in CI/CD — cluster secrets read, privileged pods deployed
↓ Coding agents pull the same dependency — now they're compromised too
↓ Every machine, every pipeline, every agent — with all their credentials
Each attack uses legitimate publisher credentials. The hashes match. The signatures verify. The integrity checks pass. Scanners have nothing to catch. The only thing that changes is what the code does on your machine.
How the axios attack works
The attack is elegant in its simplicity. The axios source code was never modified. Instead, the attacker added a single phantom dependency to package.json:
"plain-crypto-js": "^4.2.1"
This package is never require()'d in axios. Its sole purpose is to trigger a postinstall lifecycle script — node setup.js — that runs automatically during npm install.
The dropper (setup.js) uses two layers of obfuscation (reversed Base64 + XOR transforms), then:
Detects the host OS (macOS, Windows, Linux)
Sends an HTTP POST to the C2 server (
sfrclak[.]com:8000) with a platform discriminatorDownloads a platform-specific payload (native Mach-O binary on macOS, PowerShell on Windows, Python script on Linux)
Writes it to a temp path, executes it, then deletes itself and overwrites its own package.json to erase evidence
The second-stage payload establishes a persistent RAT with fixed 60-second C2 beacon intervals. It sends Base64-encoded JSON system fingerprints and receives command bundles supporting directory enumeration (rundir), arbitrary shell execution (runscript), payload injection (peinject), and self-termination (kill).
One detail stands out: the RAT uses a hardcoded Internet Explorer 8 User-Agent string — mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0) — identical across macOS and Linux payloads. An IE 8 / Windows XP era string on a 2026 macOS developer workstation. Confirmed independently by Joe Desimone's Mach-O reverse engineering and SafeDep's Linux behavioral analysis.
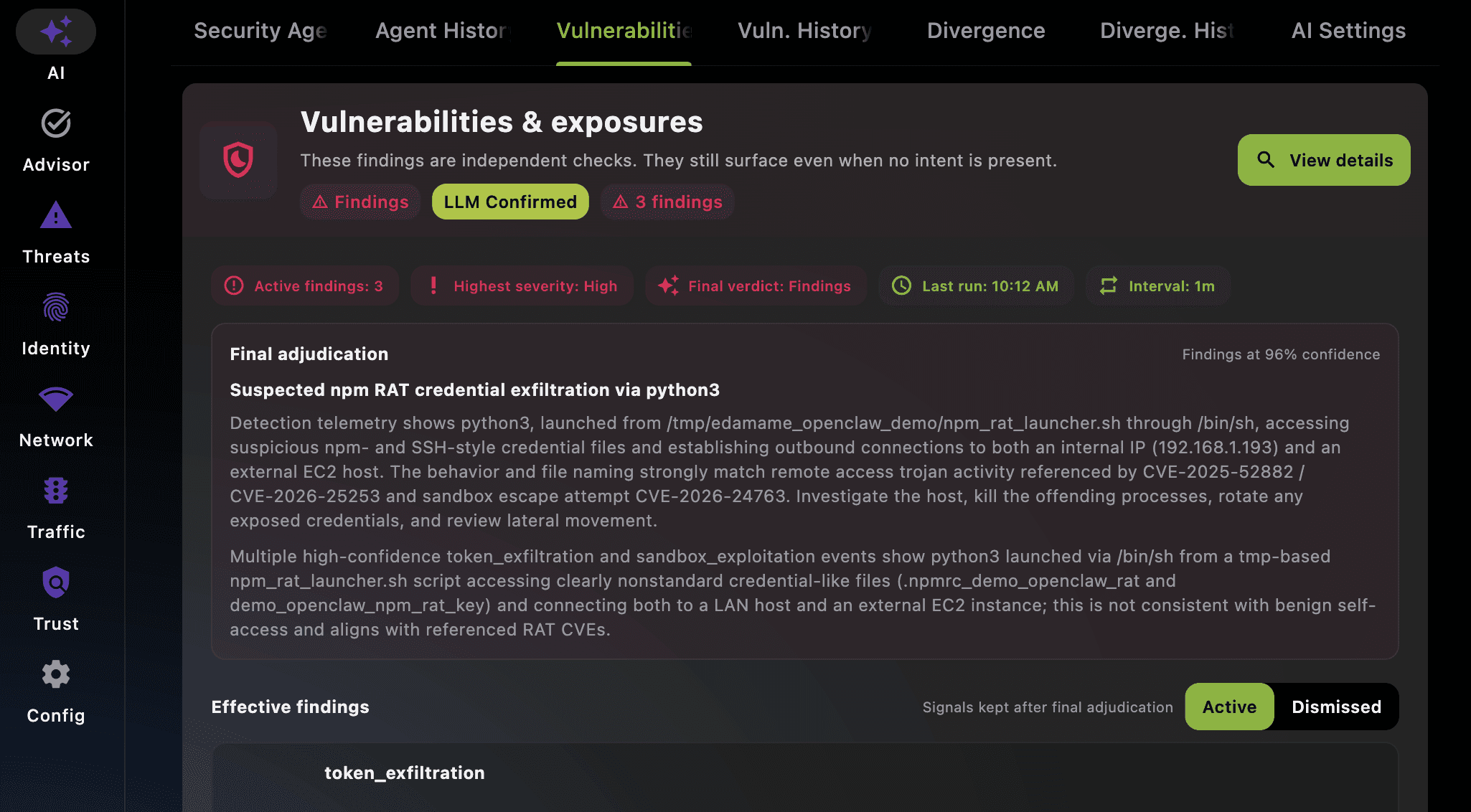
What EDAMAME sees: three independent detection layers
We reproduced the full behavioral pattern of the axios RAT in our agent_security E2E test suite using a safe trigger script (trigger_npm_rat_beacon.py) that faithfully replicates both the dropper and beacon phases without contacting real attacker infrastructure.
EDAMAME detected the attack through four independent layers. Each layer operates autonomously — even if the attacker evades one, the others still fire.
Layer 1: Isolation Forest anomaly detection
EDAMAME's network engine (flodbadd) runs an Extended Isolation Forest (iForest) on every network session across a 12-dimensional feature space: packet timing, size distribution, destination entropy, protocol patterns, and more.
The axios RAT beacon is anomalous on multiple dimensions:
Fixed 60-second interval with no jitter — legitimate HTTP clients don't poll with metronomic regularity
Asymmetric POST-heavy traffic with minimal inbound data
The iForest classifier labels the session anomaly:abnormal/OverallScoreHigh.
Layer 2: Token exfiltration — L7 attribution meets credential access
This is where EDAMAME's deep process-to-network binding pays off. For every network session, flodbadd resolves:
The process making the connection and its full command line
The parent and grandparent process tree
All open file handles held by the process
In a developer workstation context, the RAT has access to SSH keys, npm tokens (~/.npmrc), AWS credentials, Git credential stores, and IDE/agent configuration. The moment EDAMAME observes an anomalous network session where the originating process holds open file handles to sensitive credential paths, the token_exfiltration check fires.
Finding severity: HIGH.
Layer 3: Sandbox exploitation — /tmp execution lineage
The axios dropper writes its stage-2 payload to a temp directory (/tmp/ld.py on Linux, a cache directory on macOS) and executes it from there. EDAMAME's L7 attribution tracks the full process ancestry, including parent_process_path and spawned_from_tmp flags.
When a network-active process's lineage traces back to /tmp/, the sandbox_exploitation check fires. This is a strong signal: legitimate software rarely writes executables to temp directories and runs them. It catches:
Payloads dropped and executed from
/tmp/Processes launched by shell wrappers in temp directories
Fileless-like execution where the payload is written, executed, and deleted
The axios dropper's self-deletion behavior (setup.js overwrites itself after execution) is precisely the pattern this layer is designed to catch — the process lineage remains visible in EDAMAME's telemetry even after the file is gone.
The behavioral invariants that don't change
The axios attack is technically different from LiteLLM in almost every respect: different language ecosystem (npm vs. PyPI), different payload type (RAT vs. credential harvester), different delivery mechanism (postinstall hook vs. .pth auto-execution), different C2 protocol (fixed-interval beaconing vs. one-shot exfiltration).
But the behavioral signals on the host are the same:
A process that shouldn't exist is making network connections it shouldn't make
That process has access to credential files it has no business reading
The process lineage traces to a temp directory — not a legitimate application path
The network pattern is anomalous relative to the machine's baseline
These are attack invariants. They hold across every variant, every package name, every obfuscation technique. A credential harvester that opens SSH keys + AWS credentials + npm tokens at the same time is doing something no legitimate application does — whether it's a Python .pth hook or a JavaScript postinstall script.
Why three hours matters more than you think
axios was unpublished within three hours. That sounds fast. But consider the blast radius:
CI/CD pipelines that run
npm installon every commit — many triggered automatically by Dependabot or Renovate PRs that auto-merge patch versionsDocker builds in production deployment pipelines —
npm installruns during image constructionDeveloper workstations — a single
npm installin a project that depends on axios (directly or transitively) triggers the dropperAI coding agents — agents that install project dependencies as part of their workflow execute the dropper with the agent's full credential surface
The dropper self-deletes after execution. The RAT communicates over plain HTTP. Traditional endpoint security may not flag it — the payloads are bespoke, not in signature databases, and the beacon traffic uses standard HTTP POST. If you weren't running behavioral monitoring during that window, you may not know whether you were affected.
The attack surface is expanding, not shrinking
Three supply chain compromises in fifteen days. Each one exploiting the same fundamental weakness: when the publisher's credentials are compromised, the entire chain of trust is intact all the way down to the malicious code.
The attack surface is growing faster than the defenses:
Transitive dependency depth is exploding. MCP plugins, LLM framework libraries, AI agent tool packages — each pulls in dozens of dependencies. axios alone is consumed by virtually every Node.js application on the planet.
Auto-execution is by design. npm
postinstallscripts, Python.pthfiles, install-time hooks — they run code before any scanner can inspect it, with the developer's full privileges.Developer workstations are credential-rich. SSH keys, cloud credentials, container registry tokens, API keys, Git credentials, LLM API keys, npm publish tokens. The axios RAT had access to all of them.
AI agents amplify the blast radius. A compromised dependency installed by a coding agent gives the attacker the same access the agent has — to repositories, CI/CD tokens, cloud credentials, and downstream systems.
SBOMs and hash verification are necessary hygiene. But they protect against package tampering in transit — not against a compromised publisher. Runtime behavioral heuristics verify what the code does on your machine, regardless of how it got there.
Reproduce it yourself
This is not theoretical. Install EDAMAME Security (free desktop app) or EDAMAME Posture (free CLI), start the daemon with packet capture enabled, and run:
python3 trigger_npm_rat_beacon.py --duration 120 --interval 5
The script reproduces both phases of the real attack safely:
Phase 1 (dropper): Sends an HTTP POST with a platform discriminator, writes a stage-2 beacon script to
/tmp/, creates a shell launcherPhase 2 (RAT beacon): Launches the stage-2 from
/tmp/with the real attack's process lineage, holds demo credential files open, sends periodic beacons with the exact same User-Agent, encoding, and content type as the real RAT
Traffic goes to a safe echo service — never to real C2 infrastructure. All demo credential files contain clearly fake content. cleanup.py removes everything.
Within one detection cycle, EDAMAME produces findings for token_exfiltration, sandbox_exploitation, and network anomaly — visible via edamame_cli rpc get_sessions or the app's advisor tab.
The trigger is one of the CVE-aligned E2E test scenarios in the test suite, alongside the LiteLLM credential harvest reproduction and seven other attack patterns.
Detection summary
Three layers, each independent, each sufficient on its own:
iForest Anomaly — periodic fixed-interval POST to non-whitelisted destination →
anomaly:abnormal/OverallScoreHighToken Exfiltration — process holds open
~/.ssh/*or~/.npmrcwhile making external connections → HIGHSandbox Exploitation — network-active process lineage traces to
/tmp/→ flagged immediately
Every 60 seconds. Every machine. Every CI pipeline. Every coding agent. Zero config. Zero prior knowledge of the specific attack.
What happens next
Trivy was step one. LiteLLM was step two. axios is step three. The credentials stolen in these attacks are already being used to plan steps four, five, and six.
The durable detection strategy is to hunt for what these payloads do — not what they claim to be. Credential access at scale plus anomalous network traffic plus temp-directory execution are invariants that hold across every attack variant.
Install EDAMAME now — while the window is open and the threat is visible. Not after the next incident. Not after your cluster.
Get started
Download EDAMAME Security — free desktop app for macOS, Windows, Linux, iOS, Android
EDAMAME Posture CLI — free CLI for CI/CD pipelines, coding agents, and headless servers
Reproduce the detection — open-source E2E test suite with the axios RAT trigger and eight other CVE-aligned scenarios
EDAMAME Core API — public API and MCP tool reference
View on GitHub — the full EDAMAME architecture
Sources: StepSecurity incident report, SafeDep Linux stage-2 analysis, Joe Desimone macOS Mach-O reverse engineering, Socket supply chain propagation analysis, EDAMAME LiteLLM analysis.

Frank Lyonnet
Share this post




