Tech Leaders
Endpoint Security That Unleashes Your Devs
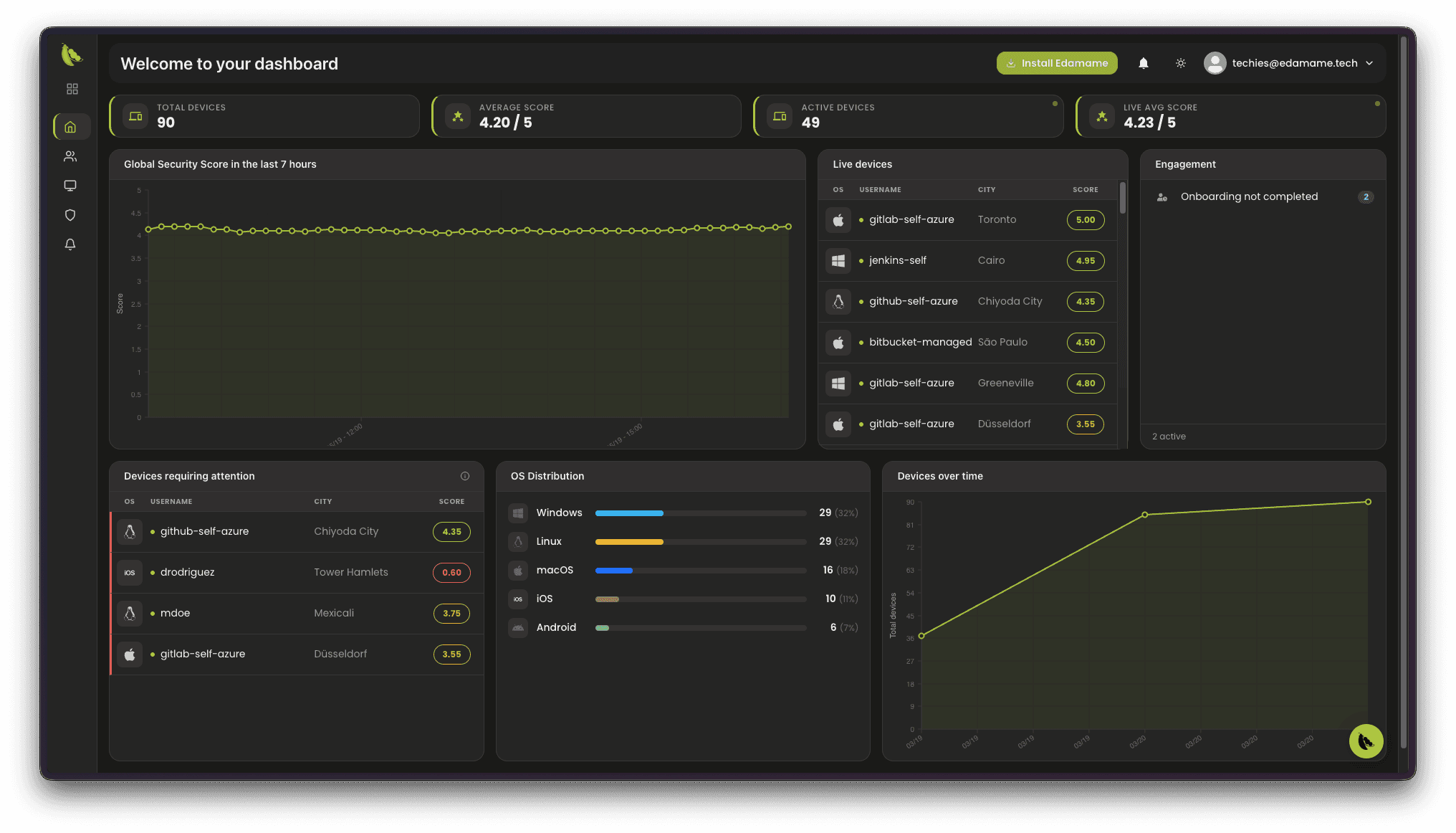
Shift security to where work actually happens — at the endpoint. EDAMAME brings endpoint-native AI Detection & Response (AIDR) to the SDLC: developers and contractors become first-response defenders, while independent host evidence — observed from outside each coding agent — turns into posture-based, audit-ready access, with no remote device control required.
Features
Holistic security for every endpoint
The industry is converging on unified, identity-first security architectures — and on AI Detection & Response (AIDR) as the EDR → XDR → AIDR next step. EDAMAME delivers the agent slice at the endpoint: see every developer, runner, and coding agent and what it touched, prove behavior against declared intent from independent host evidence, and enforce posture-gated access when something diverges — without MDM lockdown, and complementing the EDR and SOC tools you already run. Findings map to the OWASP GenAI Agentic and LLM Top 10, export to your compliance platforms, and generate SOC 2 and ISO 27001 reports. Proof, not promises.


End-user onboarding
Manage the full lifecycle of users of your corporate resources—employees or contractors—with app invites, rollout visibility, and optional self-service enrollment for approved work addresses.

Endpoint compliance
Fleet-wide endpoint compliance checks against ISO 27001, PCI DSS and SOC 2, with telemetry-backed evidence views fit for auditor review—continuity, not a staged moment.

Endpoint security posture
Gather holistic insights and events on endpoint security posture across the SDLC—for every endpoint touching code or secrets—with attention to whether AI agents show signs of tampering.


Device inventory
Explore workstations, runners and coding-agent hosts across your SDLC in one catalogue—split workstation and CI/CD views when separating interactive machines from automation makes operations simpler.


Device-based access control
Wire Hub policies into your conditional access solutions so access is granted or denied from endpoint posture, with clear room for exceptions and optional notifications when something drifts.


Device security troubleshooting
Collaborate from the same facts the user sees so they can uplevel their security posture while remediation stays local on the device—confidentiality fully preserved.
Zero Trust
Secure any SDLC environment with EDAMAME. Seamlessly integrate with source control using a Zero Trust approach with Identity Providers, native access control, and network-based access control. EDAMAME Hub gives you posture-based access and audit-ready visibility across environments—without remote device control.
Zero Trust

Manifesto
Our Manifesto for Tech Leaders: User-up Security elevates your SDLC
Decentralized cybersecurity is no longer a choice -- it is a necessity. To keep pace, organizations must evolve from rigid, admin-down control to an empowered model where teams can respond instantly at the point of action. EDAMAME makes this shift possible, giving technology leaders a way to share SDLC security responsibility with developers while maintaining full visibility and strategic oversight.
Security Without Undermining Productivity
EDAMAME hardens what matters without removing admin rights or forcing VDI. The AI assistant provides contextual guidance and one‑click fixes, so dev velocity stays high while risk stays low.
Security Beyond Compliance
Move from quarterly checklists to continuous posture. Device‑side audits, network scanning, and AI/ML traffic analysis surface issues early; signed reports map to SOC/ISO expectations when you need them.
No Admin Abuse, Ideal for Contractors
Your legal and privacy posture matters. EDAMAME is reporting‑only—no remote wipe, no covert changes. Contractors and partners stay cooperative because we verify outcomes (posture), not seize control.
Zero Trust Integration
EDAMAME integrates Identity Providers, repos, VPNs and network devices to enforce conditional access. Only secure, recognized endpoints and monitored coding agents can access critical resources. Each agent is observed independently from outside, at the endpoint boundary, and its behavior is correlated against declared intent from host evidence — aligning zero-trust principles with endpoint-native AIDR.
Versatile for CI/CD, Coding Agents and Dev Machines
One product language across laptops, runners, and coding agent infrastructure. Same posture signals, same attestations, same access rules -- less policy drift, more clarity.
Trusted by developers, open-core
Open‑core and developer‑first. The assistant speaks plain language; developers fix locally and learn along the way. Culture shifts from avoidance to practice.
From Github audit log to risk score
Understand GitHub access through what your audit log already records. Connect Hub via the read-only GitHub App: security score (0–100), actor insights, investigation-ready audit-log events—in minutes—with nothing deployed on laptops or runners.
Compliance
EDAMAME integrates seamlessly with compliance automation frameworks by exporting real-time device security assessments to third-party platforms like Vanta. Its unique approach makes it ideal for both company-owned and personal devices. Organizations can feed continuous device posture data into their compliance workflows, enhancing visibility and control. This integration supports frameworks such as SOC 2 and ISO 27001, streamlining evidence collection and audit readiness.
Testimonials
We understand the delicate balance between enabling innovation and maintaining robust security. These testimonials reinforce our commitment to empowering organizations with solutions that enhance security without compromising productivity or agility.