
Developer devices
Secure the machine and the coding assistant on it
EDAMAME Security explains what is risky on your workstation, guides hardening without taking away developer autonomy, and becomes the local trust anchor for Cursor, Claude Desktop, Claude Code, and Codex running on the same machine.
Workstation trust
Developers should keep speed, autonomy, and proof
Keep your tools, IDEs, and admin rights. EDAMAME verifies your device posture continuously, produces the proof your security team needs, and adds workstation-level evidence for local coding assistants. Runtime visibility shows when agent behavior diverges; vulnerability findings show when code touches sensitive paths or exfiltrates tokens.
Secure my machine
Harden macOS, Windows, Linux, iOS, or Android with guided fixes that respect how developers actually work.
Secure my coding assistant
Use EDAMAME Security as the workstation trust anchor for local coding sessions in Cursor, Claude Desktop, Claude Code, and Codex, then route deeper runtime verification through the agent integrations page.
Produce posture proof
Generate clear, signed posture evidence when clients, internal teams, or security reviewers need proof instead of screenshots and promises.
Features
Workstation security that helps instead of blocking
Understand the posture of your laptop or tablet, take action with guided remediation, and keep a trustworthy workstation underneath your developer tools and local coding assistants. EDAMAME reduces risk without turning the machine into a locked-down appliance, while surfacing divergence evidence and vulnerability findings when runtime behavior changes. EDAMAME has already caught real incidents in the wild—including supply chain attacks like the ones on Trivy and LiteLLM.

Keep Track of Your Agents
Track every running coding agent and raise a divergence alarm when declared intent does not match observed system actions.

Active Vulnerability Detection
Behavioral invariants on live sessions catch credential harvesting, token exfiltration, malicious skills, sandbox abuse, and file tampering—without relying on CVE feeds alone.
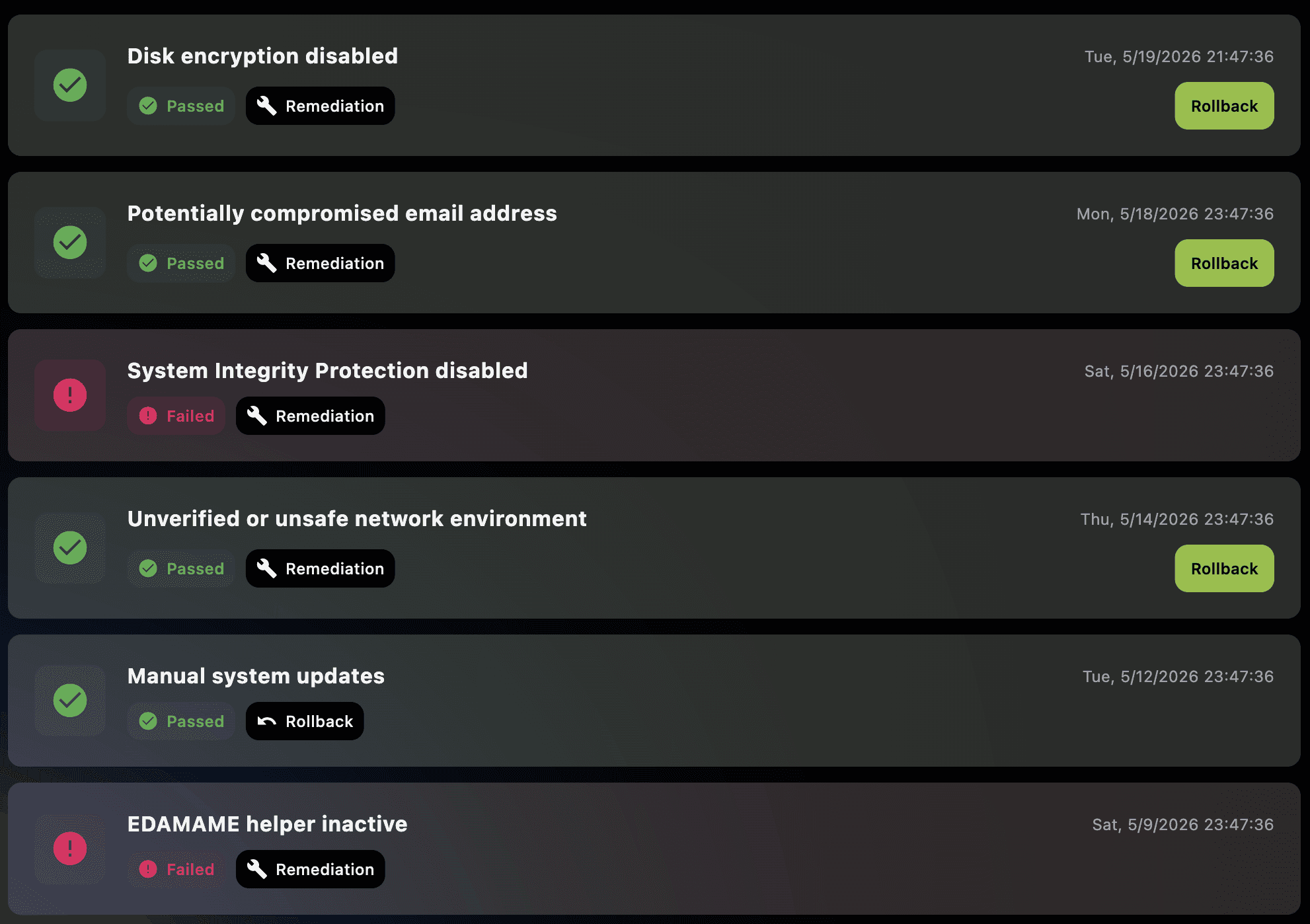
Automated Audits and Hardening
Continuous checks against OS best practices; guided remediations (enable firewall, harden services, apply patch) with user‑approved changes.
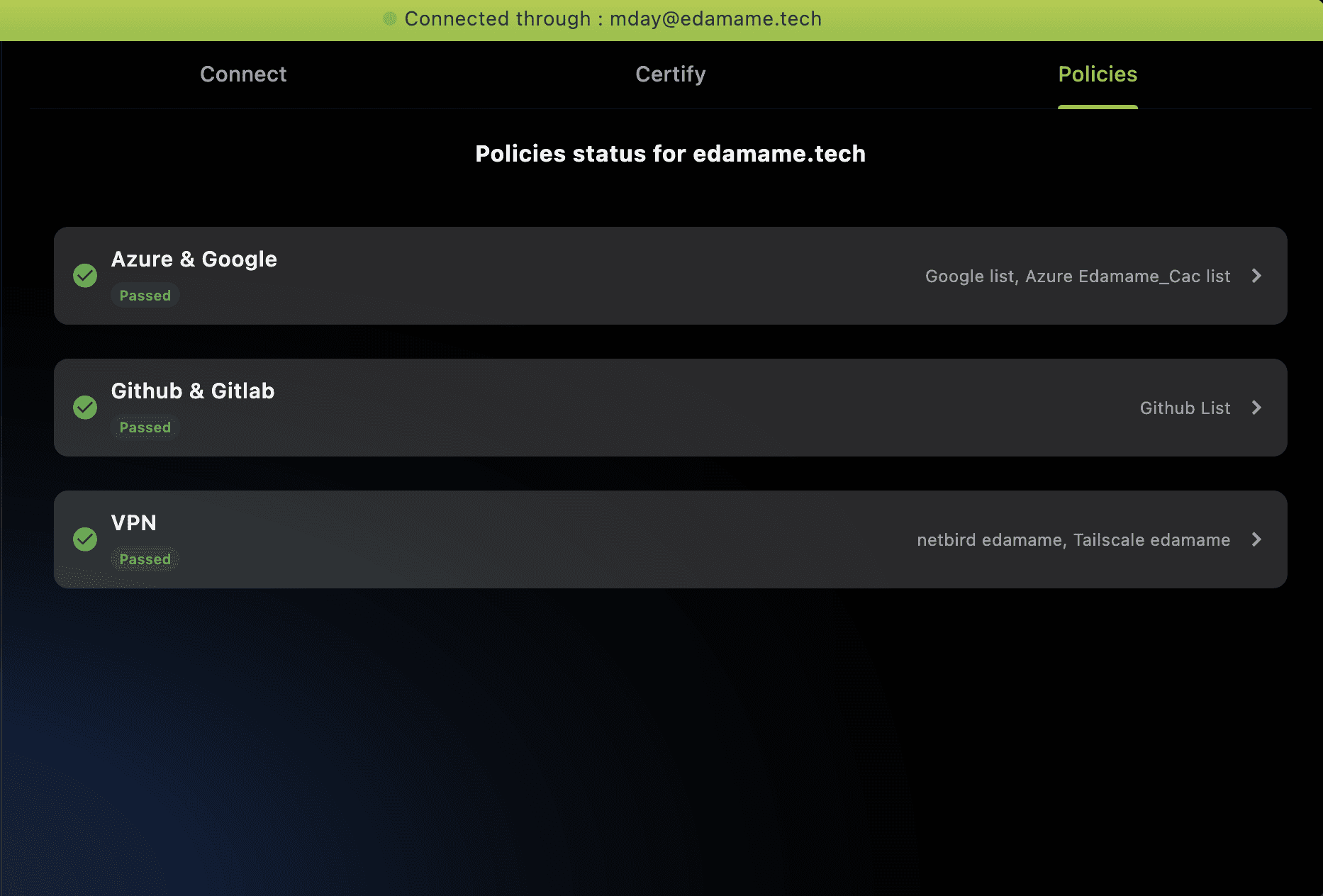
Produce Signed Compliance Reports
Click to produce ISO/SOC‑aligned posture reports for clients and security teams. Proof over promises.
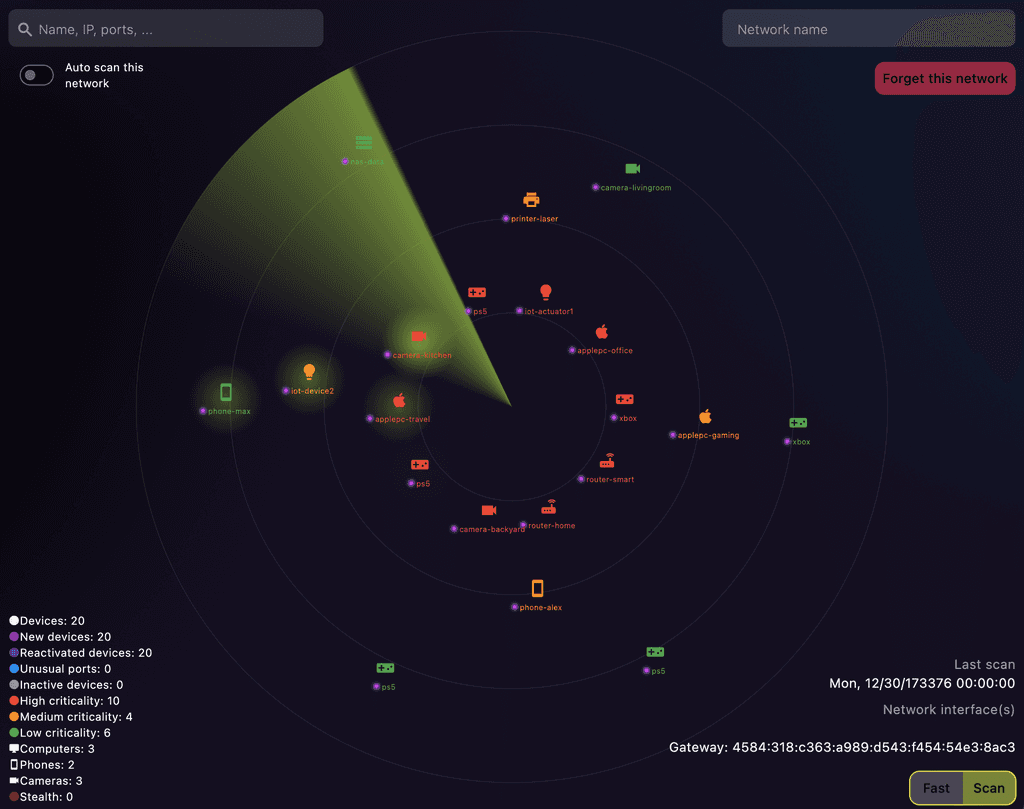
Advanced Network Scanning with AI Analysis
Discover neighbors, find exposed services, and get plain‑language guidance to reduce your attack surface.
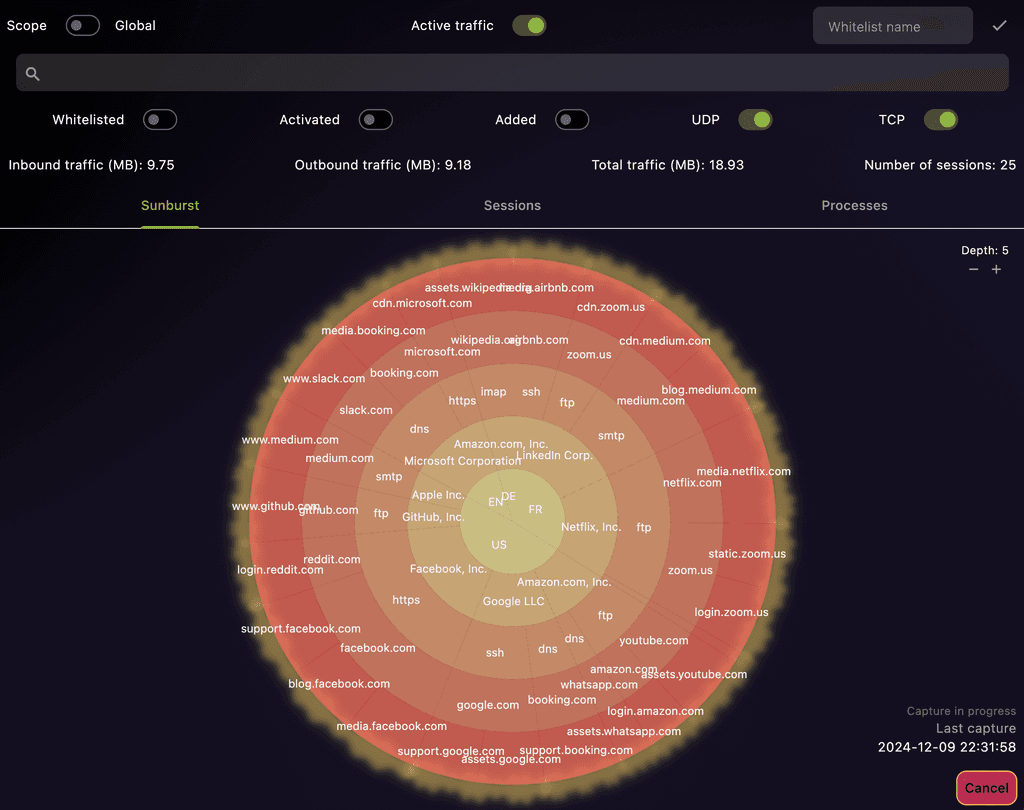
AI and ML based Process-Level Network Traffic Analysis
See which process talks to whom. ML flags anomalies; the AI explains potential risk and suggests next steps.
Who?
Who Is EDAMAME Security For?
Whether company‑held, contractor‑owned, or BYOD, EDAMAME helps you prove your device is safe—with an AI coach that keeps you compliant without slowing you down.
Developers and Software Engineers
Secure your development environments and protect your code integrity. Use this tool to ensure your systems are hardened and your applications are developed on secure platforms.
Contractors and Consultants
Safeguard sensitive client data and comply with varying security requirements. We help you secure your devices when working with multiple clients, ensuring confidentiality and maintaining professional trust.
Security Professionals and System Administrators
Enhance your toolkit with automated audits, system hardening, and advanced network analysis to maintain secure infrastructures.
Freelancers Handling Sensitive Data
Protect client information with robust security measures and proactive monitoring.
Individuals Concerned About Privacy and Security
Maintain control over your digital footprint and device integrity with professional-grade tools.
BYOD Users in Multiple Work Environments
Ensure your personal devices meet security standards across different employers and network environments.
Testimonials
As developers, we know firsthand the struggle of balancing security with productivity. These testimonials validate our mission: building developer-first tools that protect without slowing you down—empowering innovation while strengthening security in the background.





