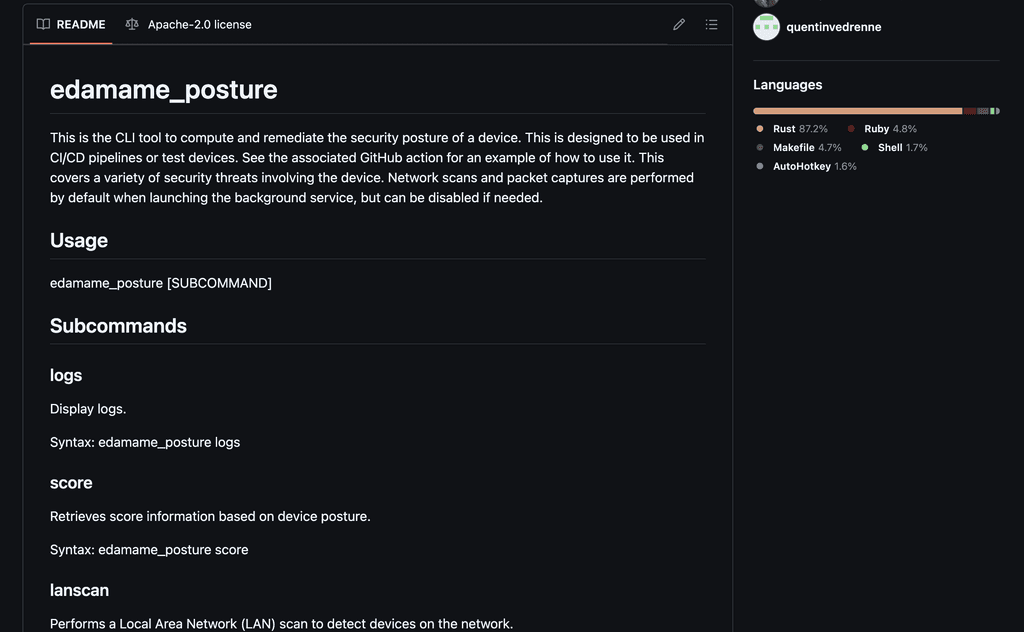
EDAMAME Posture
Secure runners, build hosts, and self-hosted coding agents
Use EDAMAME Posture to harden CI/CD runners and build hosts, then extend the same host-trust model to OpenClaw servers and other self-hosted agent environments. Runtime findings detect credential harvest, token exfiltration, and suspicious package behavior where unattended code runs.
Two lanes
One control surface for runners and self-hosted agents
Stop suspicious egress and fail builds when behavior violates allowlisted destinations. EDAMAME Posture turns supply-chain response from post-mortem into measurable runtime evidence across CI/CD runners, build hosts, and self-hosted agent servers.
Runners and build hosts
Run posture checks before secrets, builds, and deploys. Keep Linux, macOS, and Windows runners aligned with the policy you expect.
Policy gates and posture proof
Turn host trust into automated gates for repository access, secrets access, and build approvals without inventing a separate security workflow.
Self-hosted agent hosts
Use the same EDAMAME Posture foundation to harden OpenClaw servers and isolated VMs, then layer runtime verification and vulnerability findings for defense in depth.
Features
Harden the host. Layer runtime detection on top.
Measure pipelines failed due to network policy violations. Track mean time to detect anomalous egress, credential harvest, and token exfiltration during CI jobs. Lane A is CI/CD posture hardening for runners and build hosts. Lane B is self-hosted coding-agent infrastructure with runtime evidence and vulnerability findings.