
Audit log scoring
Understand GitHub access in one screen
Get a security score, actor insights, and investigation-ready events from your GitHub audit log — in minutes.
Free for all Hub users · Read-only GitHub App · No device deployment · Results in minutes
GitHub logs have everything. Except answers.
Your audit log records every clone, push, token use, and permission change. But there’s no scoring, no actor classification, and no way to investigate fast.
Who accessed private repos?
Which tokens are active?
What changed in permissions?
Where are Git operations coming from?
THE FIX
One report. Every answer.
Connect a read-only GitHub App. Choose a lookback window (7–180 days). Get a scored report with actor breakdown and investigation-ready events.
Security teams export CSV files and manually search for signals. Critical questions go unanswered for days.
Your GitHub audit — ready in minutes
Security score (0–100): Good, Needs attention, or At risk — in seconds.
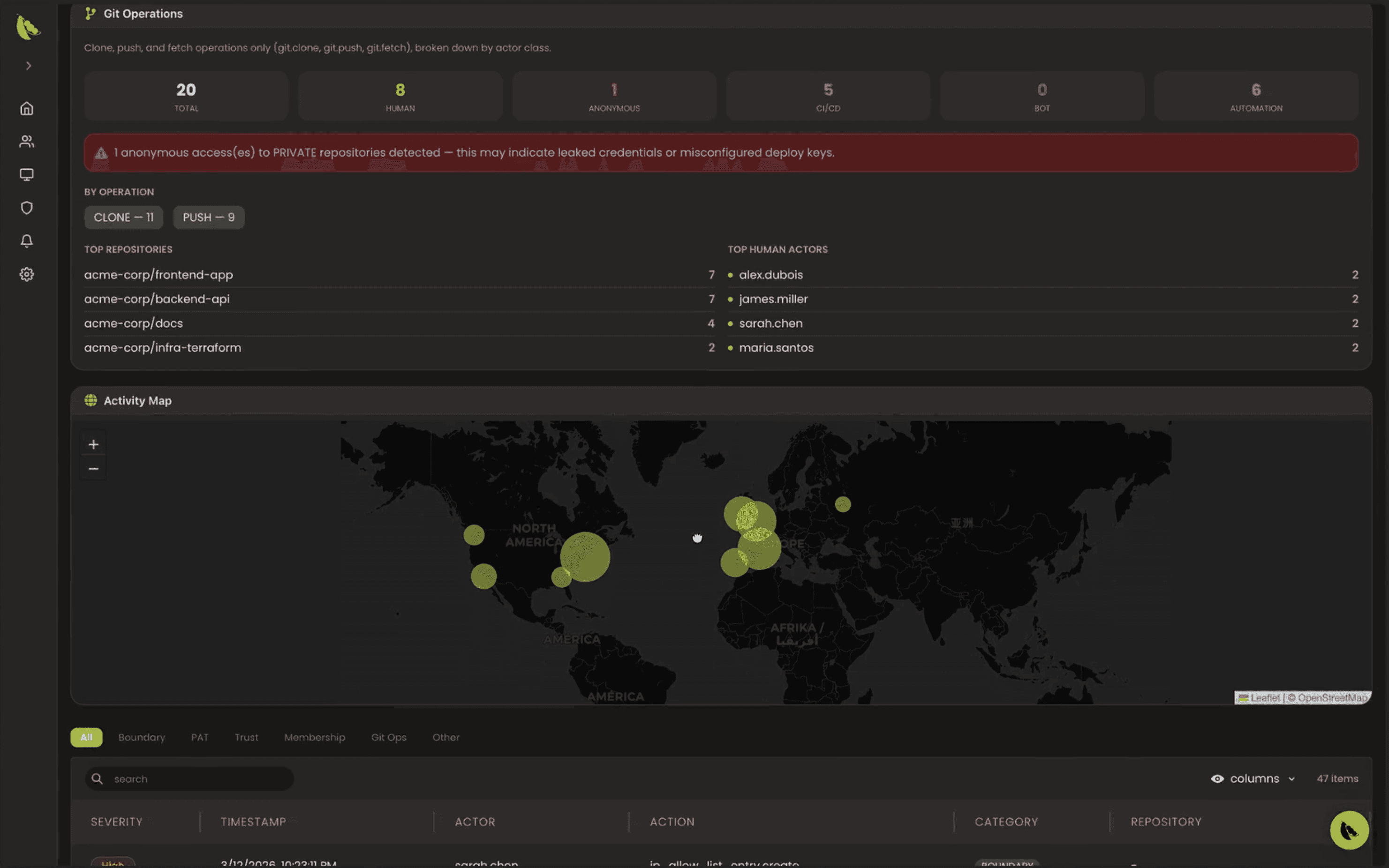
Actor analysis: human vs non-human, top actors, operation breakdown.
Investigation table: searchable, paginated events with severity and category filters.
Your GitHub audit — scored, explained, and ready to investigate.
No agents to install, no code changes, no device enrollment. Just connect GitHub and run.
Everything you need to investigate
EDAMAME Hub processes your GitHub audit log and returns an actionable report with scoring, actors, signals, and an investigation-ready event table.
See your GitHub risk in seconds
A clear 0–100 score with what needs attention.
Know who and what is accessing your code
Human vs machine actors, tokens, and activity.
Detect suspicious behavior instantly
Unusual clones, pushes, and access patterns flagged.
Investigate events without digging through logs
Search, filter, and understand activity in seconds.
Use it for the moments that matter
Whether you are responding to an incident, preparing for an audit, or baselining risk — GitHub Audit gives you answers in minutes.
01
Investigate a security incident in seconds
Without EDAMAME
Find who did what, when, and from where — instantly.
With EDAMAME
Search the event table by actor, operation, or time range — seconds to context.
02
Answer audit questions without digging
Without EDAMAME
See a clear report of activity, actors, and signals in one place.
With EDAMAME
Export a scored report with severity distribution and actor breakdown.
03
Get visibility you didn’t have before
Without EDAMAME
Surface hidden activity like token usage and unusual access.
With EDAMAME
Run a 180-day audit. Get a 0–100 score and a prioritized list of signals.


