Agent Security
Runtime security for Cursor, Claude Desktop, Claude Code, Codex, and OpenClaw
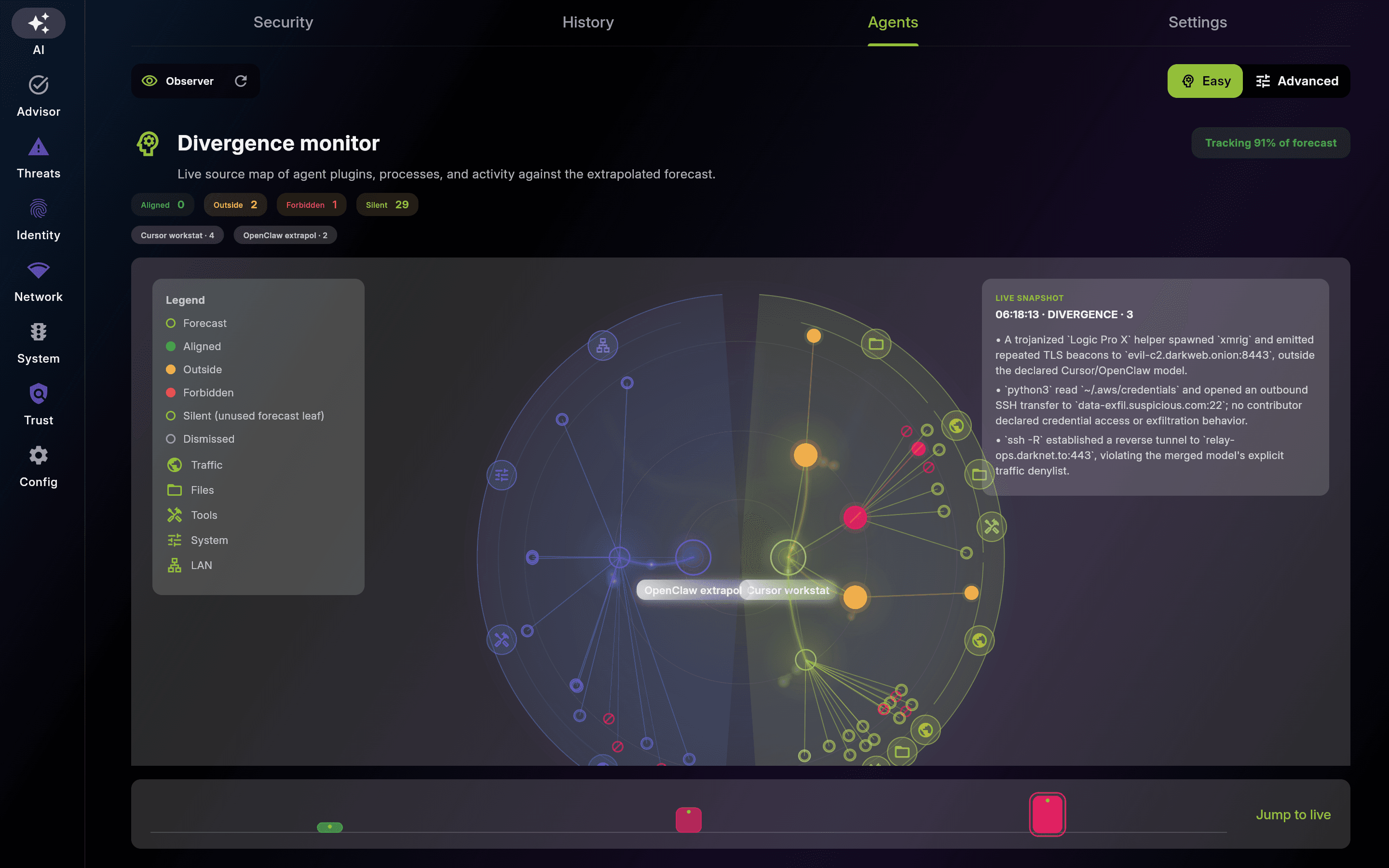
One trust layer for developer workstations, runners, and agent hosts. EDAMAME Hub finds unsecured coding-agent installs across the fleet; EDAMAME Security and EDAMAME Posture then use host evidence to score divergence between declared intent and live behavior, and to detect attack-pattern findings such as credential harvest and token exfiltration.
Why runtime verification
Static hardening matters. Runtime verification is missing.
Poisoned tools, compromised plugins, and opportunistic agentic coding are emerging risks: a coding agent can drift from its declared task while staying inside nominal policy boundaries, and a compromised dependency can harvest secrets while the package chain still looks legitimate. EDAMAME does not ask a language model to guess what happened. It starts from high-quality host signals, then applies AI to interpret, explain, and remediate. Runtime verification compares declared intent with observed behavior from endpoint truth. Attack detection uses the same telemetry to see what code opens, spawns, and sends.
Static setup is not enough
Signed tools, sandboxing, least-privilege installs, and scoped permissions reduce exposure before runtime. That setup still stops short of describing what the agent does once execution starts.
Runtime drift still happens
An agent can read external content, use allowed tools, or load a poisoned plugin and still stay inside the nominal setup while moving away from the original task.
System truth closes the gap
Unexpected traffic, new processes, file changes, posture drift, and sensitive-file access are the host-side ground truth. The same evidence makes divergence visible and attack-pattern findings actionable.
Fleet and endpoint
Discover in Hub. Prove on the workstation.
EDAMAME splits the workload into posture you can automate and verification you can trust: anchor every runner, server, or workstation, then reconcile declared coding-agent intent with observed processes, filesystem, traffic, and posture signals while detecting compromised behavior through CVE-aligned attack-pattern findings such as credential harvest and token exfiltration. Fleet-wide, EDAMAME Hub surfaces workstations and hosts running popular coding-agent stacks without that trust anchor.
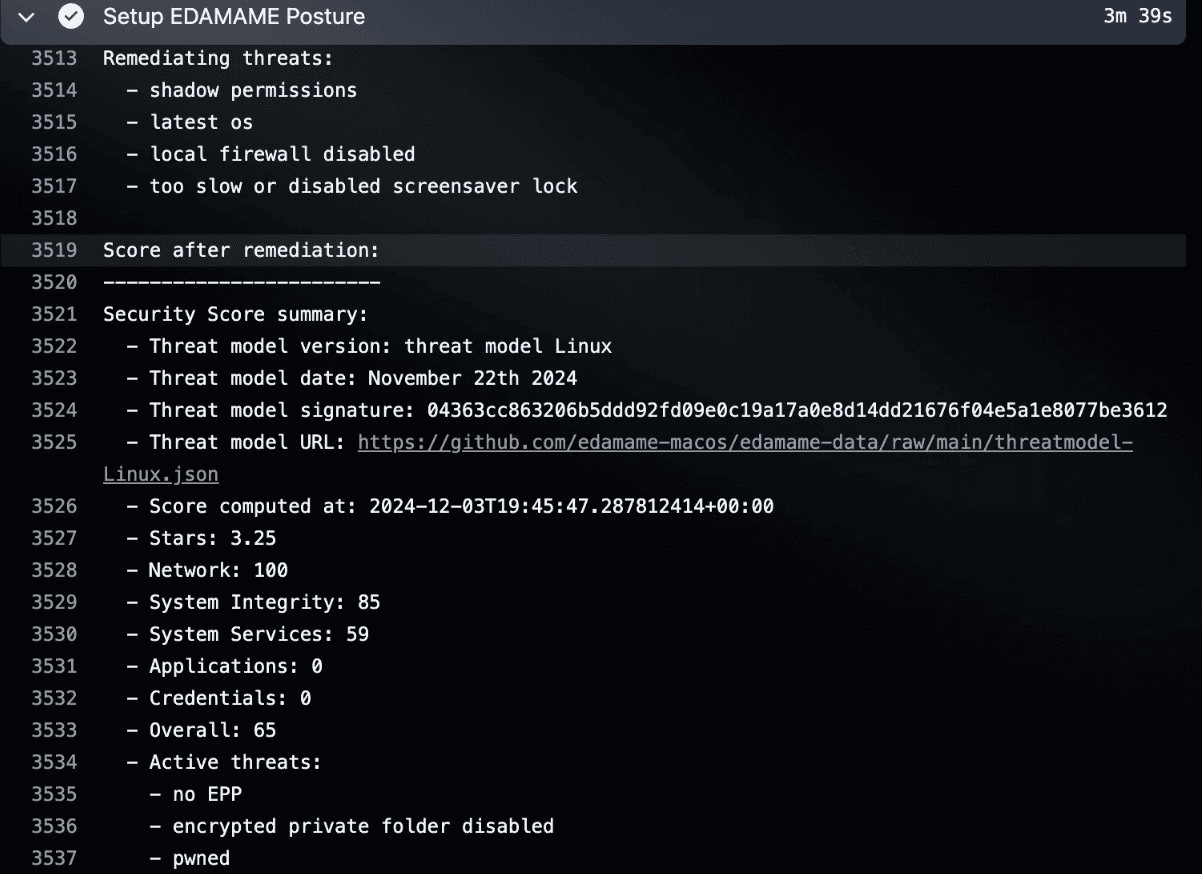
Harden the runner or agent host
Use EDAMAME Posture on CI/CD runners, servers, and self-hosted agent hosts such as OpenClaw; then reconcile the systems EDAMAME Hub identified as unmanaged with deterministic posture proofs on those machines.
• Continuous posture monitoring and scoring
• Automated hardening and policy gates
• L7 traffic visibility and escalation
• Strong foundation for self-hosted agents
Verify intent on the host
Intent evidence starts at the workstation or host. EDAMAME ingests agent-native signals beside process, file, network, and posture observations, then turns drift into attributable evidence. The same host stream feeds attack-pattern findings when code touches sensitive paths or exfiltrates tokens.
• Intent evidence: declared task and session context
• Host truth: processes, files, network, and posture
• Divergence score with an evidence trail
• Attack-pattern findings from live host telemetry
Self-hosted agents
Secure runners, build hosts, and OpenClaw servers
EDAMAME Posture secures the infrastructure behind agentic work: CI/CD runners, isolated VMs, and self-hosted coding-agent hosts. Harden the substrate; runtime verification then reconciles declared agent work with what those machines actually observe, while attack-pattern findings detect compromised packages, credential harvest, and anomalous exfiltration from the same telemetry.
Runner and build-host hardening
Patch, firewall, encryption, remote-access, and endpoint checks keep build infrastructure trustworthy before secrets or repositories are touched.
OpenClaw-ready host posture
Deploy the same CLI and posture controls on OpenClaw servers and isolated agent VMs before you rely on unattended agents. Verification attaches cleanly at the host.
Traffic, findings, and escalation
Process-attributed traffic, anomaly detection, CVE-aligned findings, and human-in-the-loop escalation help security teams inspect risky behavior without guessing.
Choose your surface
Secure the agent surface you use today
Move from invisible sprawl to a managed surface. EDAMAME Hub flags workstations and hosts running common coding-agent stacks without the EDAMAME trust anchor. Once anchored, those hosts produce divergence evidence and attack-pattern findings across Cursor, Claude Desktop, Claude Code, Codex, and self-hosted OpenClaw.
Secure Cursor and Codex on the developer workstation
Cursor and OpenAI Codex run on EDAMAME-secured workstations that EDAMAME Hub inventories fleet-wide. Correlate IDE activity with posture, filesystem, and network telemetry to score divergence and surface attack-pattern findings.
Bring runtime monitoring to Claude Desktop and Claude Code
Instrument Claude Desktop sessions and Claude Code workflows with workstation-level telemetry. Agent-native cues and host truth stay aligned while attack-pattern checks watch for sensitive-file access and exfiltration behavior.
Protect self-hosted OpenClaw environments
Harden OpenClaw servers and VMs with EDAMAME Posture, then add runtime verification and attack-pattern findings through the package, plugin bundle, and provisioning flow.